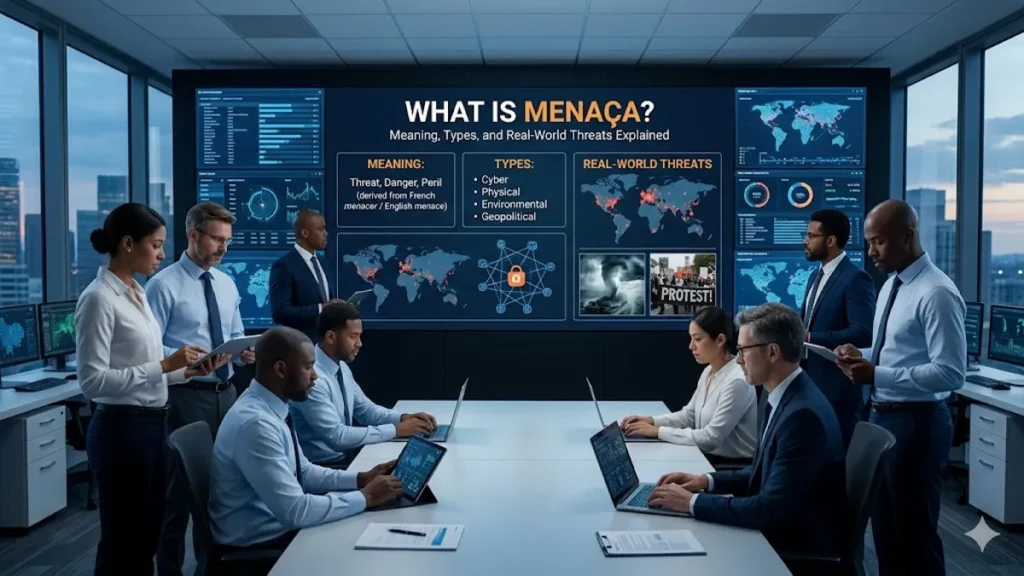
Threats shape how societies organize power, build institutions, and protect what they value. The word “menaça,” derived from Portuguese and Catalan usage, translates directly to “threat” or “menace.” At its simplest, a threat refers to the possibility of harm, whether expressed intentionally or emerging from circumstances beyond human control. Dictionaries define it as an expression or sign of potential damage or danger.
Yet the meaning of threat extends far beyond language. Governments analyze threats to national security. Businesses measure threats to assets and reputations. Individuals perceive threats in health, environment, technology, and economic stability. In modern risk analysis, a threat is typically defined as any circumstance or event capable of causing harm or loss, particularly when it can exploit vulnerabilities within a system.
Understanding threats matters because identifying them is the first step toward prevention. Analysts often describe the relationship between threat, vulnerability, and risk: threats exploit weaknesses, and risk reflects the likelihood and consequences of that exploitation.
In an increasingly interconnected world, threats are no longer isolated events. Cyber attacks can cross borders instantly. Environmental crises can destabilize economies. Disinformation campaigns can reshape political realities. From ancient warfare to modern digital infrastructure, the evolution of threats reflects humanity’s evolving systems of power, technology, and trust.
This article explores the nature of threats: how they are defined, classified, and perceived, and how governments, corporations, and individuals respond. It examines the historical roots of the concept, the rise of modern threat intelligence, and the ways societies attempt to anticipate dangers before they become disasters.
The Concept of Threat in Language and Philosophy
The concept of threat has existed as long as human conflict itself. Linguistically, the word refers to a declaration or signal of intent to cause harm. But philosophers and political theorists have long argued that threats are not simply actions; they are signals within systems of power. – menaça.
In classical political theory, threats served as tools of coercion. States used the possibility of violence to enforce laws or deter enemies. Thomas Hobbes described political authority as a structure built partly upon the implicit threat of punishment.
Modern scholars treat threats as perceptions rather than only objective dangers. A threat exists when a person or institution believes that something could damage what it values. This psychological dimension explains why societies respond differently to similar risks.
A looming storm might threaten one community more than another depending on infrastructure. A new technology might threaten established industries while benefiting emerging ones. The perception of threat therefore becomes as influential as the threat itself. – menaça.
Security studies often distinguish between three elements: a threat source, a vulnerability, and an asset at risk. When these elements intersect, the conditions for damage appear.
Dr. Bruce Schneier, a widely cited security technologist, once summarized the dynamic succinctly: “Security is not about eliminating threats entirely but about reducing the chances that they can exploit vulnerabilities.” His work in cybersecurity emphasizes that threats cannot always be controlled, but exposure can be managed.
Understanding threats therefore begins with understanding systems: what is valuable, where weaknesses exist, and who or what might exploit them.
Read: JerkRoulette Explained: Inside Random Adult Video Chat
Threat, Risk, and Vulnerability: The Security Triad
Security professionals often rely on a conceptual framework linking three fundamental elements: threats, vulnerabilities, and risks. – menaça.
Threats represent potential causes of harm. Vulnerabilities are weaknesses that allow harm to occur. Risk describes the probability and impact when threats exploit vulnerabilities.
This framework is widely used in cybersecurity, safety engineering, and corporate governance. Organizations identify assets such as data, infrastructure, or intellectual property. They then assess vulnerabilities that could expose those assets to threats.
A threat might be malicious, such as a hacker attempting unauthorized access. It might also be accidental, such as human error or equipment failure.
Security strategist Eva Galperin of the Electronic Frontier Foundation has argued that organizations often misunderstand threats because they focus too heavily on technology rather than context.
“Threat modeling is about understanding who might target you and why,” she has said in numerous cybersecurity conferences. The implication is that threats are not abstract forces but actions carried out by actors with motivations.
The relationship between threat, vulnerability, and risk can be summarized as follows.
| Element | Definition | Example |
|---|---|---|
| Threat | Potential cause of harm or loss | Hacker targeting a company network |
| Vulnerability | Weakness that enables exploitation | Outdated software with known flaws |
| Risk | Likelihood and impact of damage | Data breach exposing customer records |
In practice, organizations rarely eliminate threats entirely. Instead they attempt to reduce vulnerabilities and mitigate potential impacts.
This triad forms the backbone of modern risk management frameworks used by governments, technology companies, and international institutions.
Categories of Threats in Modern Society
Threats appear across nearly every domain of human life. Analysts commonly classify them into several major categories depending on their origin and nature.
Human-made threats include deliberate actions such as terrorism, espionage, cybercrime, and organized crime. These threats typically involve actors with clear intentions. – menaça.
Natural threats arise from environmental forces such as earthquakes, hurricanes, and pandemics. These threats lack human intent but can still cause catastrophic damage.
Technological threats emerge from failures in complex systems such as electrical grids, transportation networks, or digital infrastructure.
Economic threats involve financial instability, supply chain disruptions, and systemic market risks.
The table below summarizes common threat categories and examples.
| Threat Category | Typical Source | Example |
|---|---|---|
| Natural | Environmental forces | Earthquakes, hurricanes |
| Technological | System failures | Power grid outages |
| Human deliberate | Malicious actors | Cyber attacks, terrorism |
| Human accidental | Error or negligence | Data leaks, industrial accidents |
| Economic | Market instability | Financial crises |
Cybersecurity experts often emphasize that modern threats increasingly overlap. A cyberattack on infrastructure could trigger economic disruption, political conflict, and public panic simultaneously.
According to cybersecurity analyst Bruce Schneier, “the most dangerous threats are not isolated events but cascades across interconnected systems.” – menaça.
As societies grow more technologically dependent, these interconnected risks become harder to predict.
The Rise of Cyber Threats in the Digital Era
In the digital age, cyber threats have become among the most discussed forms of modern menace. Governments and corporations now invest billions annually in cybersecurity to protect critical infrastructure and sensitive data.
Cyber threats include malware attacks, ransomware, phishing campaigns, and espionage operations. These threats exploit vulnerabilities in computer systems to compromise confidentiality, integrity, or availability of information.
The rise of advanced persistent threats (APTs) has intensified concerns about state-sponsored cyber operations. APTs are highly sophisticated attacks conducted over long periods, often by organized groups or nation-states.
One of the most famous examples occurred in 2010 with the discovery of the Stuxnet worm, widely believed to have targeted Iranian nuclear facilities. The incident demonstrated that cyber threats could produce real-world physical consequences.
Cybersecurity strategist Dmitri Alperovitch, co-founder of CrowdStrike, once noted that “cyber conflict has become the fifth domain of warfare, alongside land, sea, air, and space.”
The implications are profound. Digital infrastructure now underpins banking, transportation, healthcare, and communication systems. – menaça.
As a result, cyber threats increasingly rank alongside traditional military threats in national security strategies.
National Security and the Politics of Threat
Threat perception often drives political decision-making. Governments justify military budgets, surveillance programs, and diplomatic alliances by identifying potential dangers to national stability.
During the Cold War, the dominant threat narrative centered on nuclear conflict between superpowers. The doctrine of mutually assured destruction functioned as both deterrence and existential danger.
In the twenty-first century, threat landscapes have become more complex. Governments face a mixture of traditional military threats and unconventional ones, including cyber warfare, terrorism, and disinformation campaigns.
Political scientist Barry Buzan argues that security threats can also be socially constructed. Leaders sometimes frame issues such as migration or economic competition as threats to justify extraordinary policies.
This process, known as securitization, transforms political debates into matters of survival.
The result is a paradox: threats may exist objectively, but how societies respond often depends on perception, political narratives, and media coverage. – menaça.
Environmental Threats and the Climate Crisis
Few modern threats illustrate global interdependence as clearly as climate change. Environmental scientists increasingly describe climate disruption as a “threat multiplier,” intensifying existing risks such as food insecurity, migration pressures, and political instability.
Rising sea levels threaten coastal cities. Heat waves strain energy infrastructure. Droughts destabilize agricultural systems.
According to the Intergovernmental Panel on Climate Change (IPCC), global temperatures have already risen significantly since the preindustrial era, increasing the frequency of extreme weather events.
Environmental threats differ from many others because they operate over long time horizons. Their impacts unfold gradually but accumulate into systemic crises.
Former United Nations Secretary-General Ban Ki-moon once warned, “Climate change is not only an environmental issue. It is a threat to peace and stability.”
This framing has influenced military planning as well. Many defense agencies now incorporate climate scenarios into strategic forecasting.
Perception, Psychology, and the Fear of Threat
Human beings rarely evaluate threats purely rationally. Psychological research shows that people respond more strongly to dramatic dangers than to slow-moving risks.
For example, terrorist attacks often generate intense fear despite statistically lower probabilities compared to everyday hazards such as traffic accidents.
Psychologist Daniel Kahneman has explained this phenomenon through the concept of availability bias. People assess danger based on how easily examples come to mind.
Media coverage can amplify this effect. Highly visible threats may dominate public discourse even when their actual probability is relatively small.
Security experts therefore emphasize the importance of threat assessment frameworks. These tools attempt to quantify probability and impact rather than relying on intuition. – menaça.
Threat intelligence systems collect data on emerging risks, analyze patterns, and forecast possible scenarios.
While no method can eliminate uncertainty entirely, structured analysis helps organizations respond more proportionately.
Threat Intelligence and Predictive Security
Modern security strategies increasingly rely on threat intelligence. This field combines data analysis, intelligence gathering, and risk modeling to anticipate dangers before they occur.
Threat intelligence analysts monitor indicators such as cyberattack patterns, geopolitical tensions, and criminal networks.
The goal is early detection. If organizations can identify threats before they materialize, they can strengthen defenses and reduce potential damage.
Major technology companies maintain dedicated threat intelligence teams. Governments operate intelligence agencies that track both military and cyber threats globally.
One of the central principles of threat intelligence is proactive defense. Instead of reacting after damage occurs, organizations attempt to predict adversaries’ behavior.
Security researcher Marcus Ranum once described this shift as “moving from castle walls to radar systems.”
In other words, the focus has shifted from static defense to continuous monitoring.
Timeline of Major Modern Threat Developments
| Year | Event | Significance |
|---|---|---|
| 1945 | Atomic bombings of Hiroshima and Nagasaki | Introduced nuclear existential threat |
| 1991 | Rise of global internet infrastructure | Created digital threat landscape |
| 2001 | September 11 attacks | Redefined global counterterrorism strategy |
| 2010 | Discovery of Stuxnet malware | Demonstrated cyber weapons capability |
| 2020 | COVID-19 pandemic | Highlighted global biological threat |
These events illustrate how threat landscapes evolve alongside technological and political change.
Takeaways
- A threat refers to any circumstance or event capable of causing harm or loss.
- Modern security frameworks distinguish between threat, vulnerability, and risk.
- Threats may originate from natural forces, human actions, or technological systems.
- Cyber threats have become a dominant concern in the digital era.
- Perception of threat often shapes political and social responses.
- Environmental change increasingly functions as a global threat multiplier.
- Threat intelligence seeks to predict and mitigate risks before damage occurs.
Conclusion
Threats have always existed, but the scale and complexity of modern systems have transformed how societies perceive and manage them. In ancient times, threats often appeared in the form of invading armies or natural disasters. Today they can emerge from invisible networks of code, shifting climate systems, or financial markets interconnected across continents.
What remains constant is the human need to identify danger before it becomes catastrophe. Understanding threats requires more than fear; it requires analysis, context, and preparation.
Security experts emphasize that threats themselves cannot always be eliminated. Natural disasters will occur. Malicious actors will continue seeking advantage. Technologies will introduce new vulnerabilities even as they solve old problems.
The challenge lies in resilience. By identifying vulnerabilities, strengthening institutions, and improving early-warning systems, societies can reduce the damage threats inflict.
Ultimately, the study of threats is not simply about danger. It is about safeguarding the systems that sustain human life, from digital infrastructure and global economies to ecosystems and democratic institutions.
The future will inevitably bring new forms of menace. Whether societies can anticipate and manage them may determine the stability of the decades ahead.
FAQs
What does the word “menaça” mean?
“Menaça” is a Portuguese and Catalan term meaning “threat” or “menace.” It refers to a potential danger or an expression of intent to cause harm.
How is a threat different from risk?
A threat is a potential source of harm, while risk measures the likelihood and impact of that threat exploiting a vulnerability.
What are common examples of threats?
Examples include cyber attacks, natural disasters, terrorism, economic crises, and system failures.
Why are cyber threats increasing?
As societies rely more on digital infrastructure, attackers exploit vulnerabilities in networks, software, and data systems.
Can threats ever be completely eliminated?
No. Most security frameworks aim to reduce vulnerabilities and mitigate impacts rather than eliminating threats entirely.